In this course we look at the concept reconnaissance. We will cover the basic principles of reconnaissance, differences between passive and active reconnaissance, reconnaissance tools and the course ends with a quiz.
What is Reconnaissance?
Reconnaissance is a concept that is known for centuries, primarily for military strategical purpose.
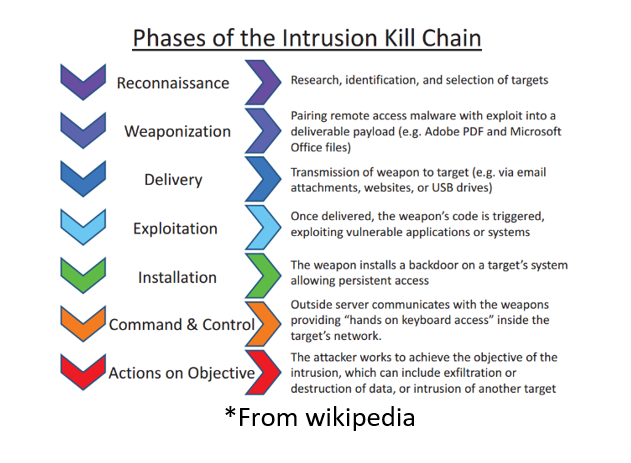
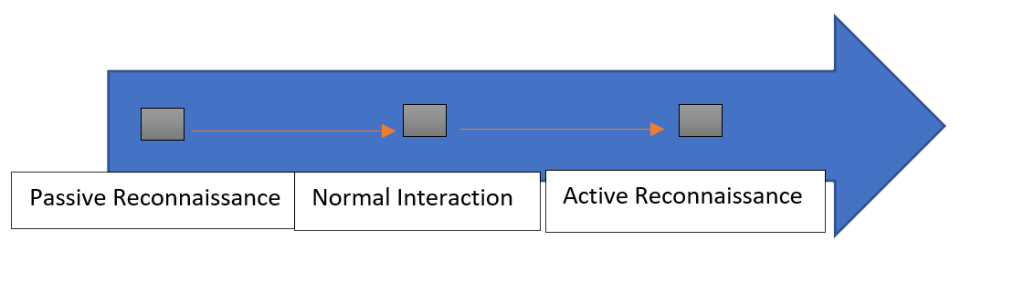
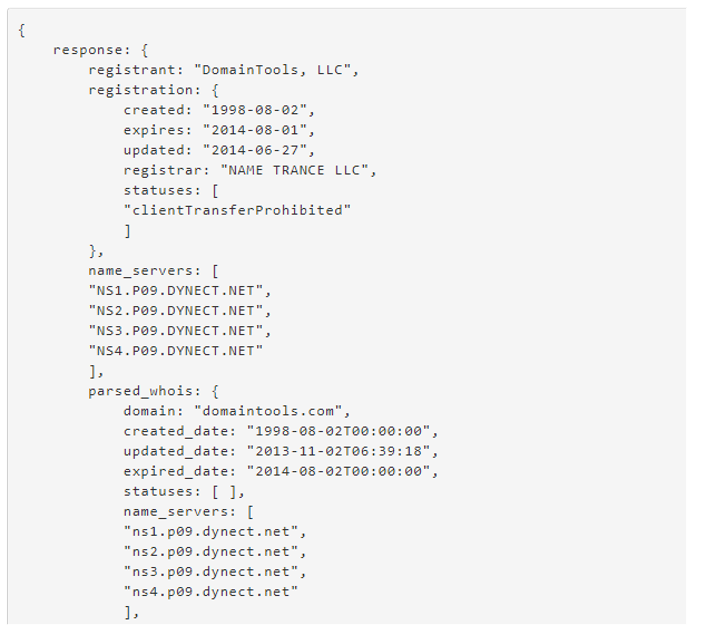
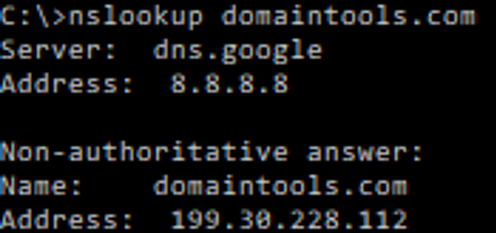
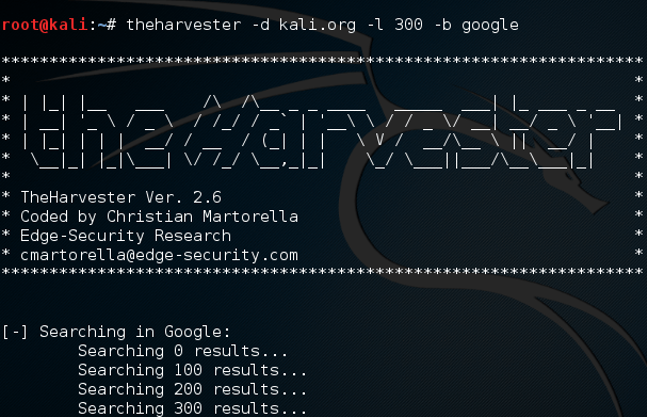
In IT security it is an important phase, in which an attacker uses for obtaining detailed information about their target. By using specific tools(which will be presented later in this course) for this phase of the attack, the attacker can interact with potential open ports, services running, etc on the targets network/systems or attempt to gain information without actively engaging with the network.